You receive a clear, developer-focused report that includes:
- Verified exploitable vulnerabilities
- Step-by-step reproduction details
- Business impact (real risk, not generic severity)
- Practical remediation guidance
No noise. No automated scan dumps.
Manual Penetration Testing for SaaS, APIs, and Modern Web Applications
At The Hidden Finds, we help SaaS companies identify real, exploitable vulnerabilities through manual web application penetration testing. Our focus is on uncovering security issues that attackers actually abuse — not just theoretical findings.
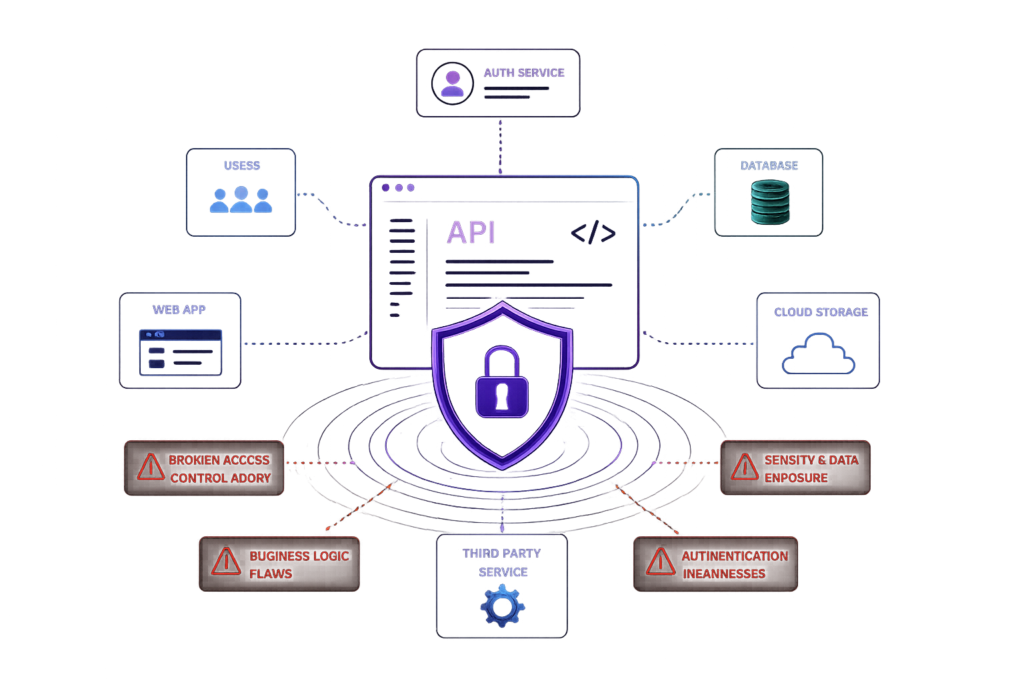
We test authentication systems, APIs, access controls, and business logic to identify critical vulnerabilities such as IDOR (Broken Access Control), session weaknesses, insecure workflows, and sensitive data exposure.
Unlike automated scanning tools, our approach is fully manual — allowing us to uncover complex attack paths, chained vulnerabilities, and real-world security risks that often go undetected.

“Focused on real-world exploitability — not theoretical findings.”
Our web application penetration testing methodology is built around real-world attack simulation and manual security testing — not automated scan reports. We assess application behavior by testing authentication mechanisms, API endpoints, session handling, and access control logic to identify vulnerabilities that can be actively exploited by attackers.
Our testing covers critical issues such as broken access control (IDOR/BOLA), insecure authentication flows, business logic vulnerabilities, and data exposure risks — the same weaknesses responsible for account takeovers, data breaches, and real-world security incidents.
By focusing on practical exploitation scenarios, we help your team understand true risk, prioritize remediation, and fix vulnerabilities that directly impact your business. We go beyond surface-level testing — analyzing how attackers interact with your application to uncover hidden attack paths, chained vulnerabilities, and complex security flaws.
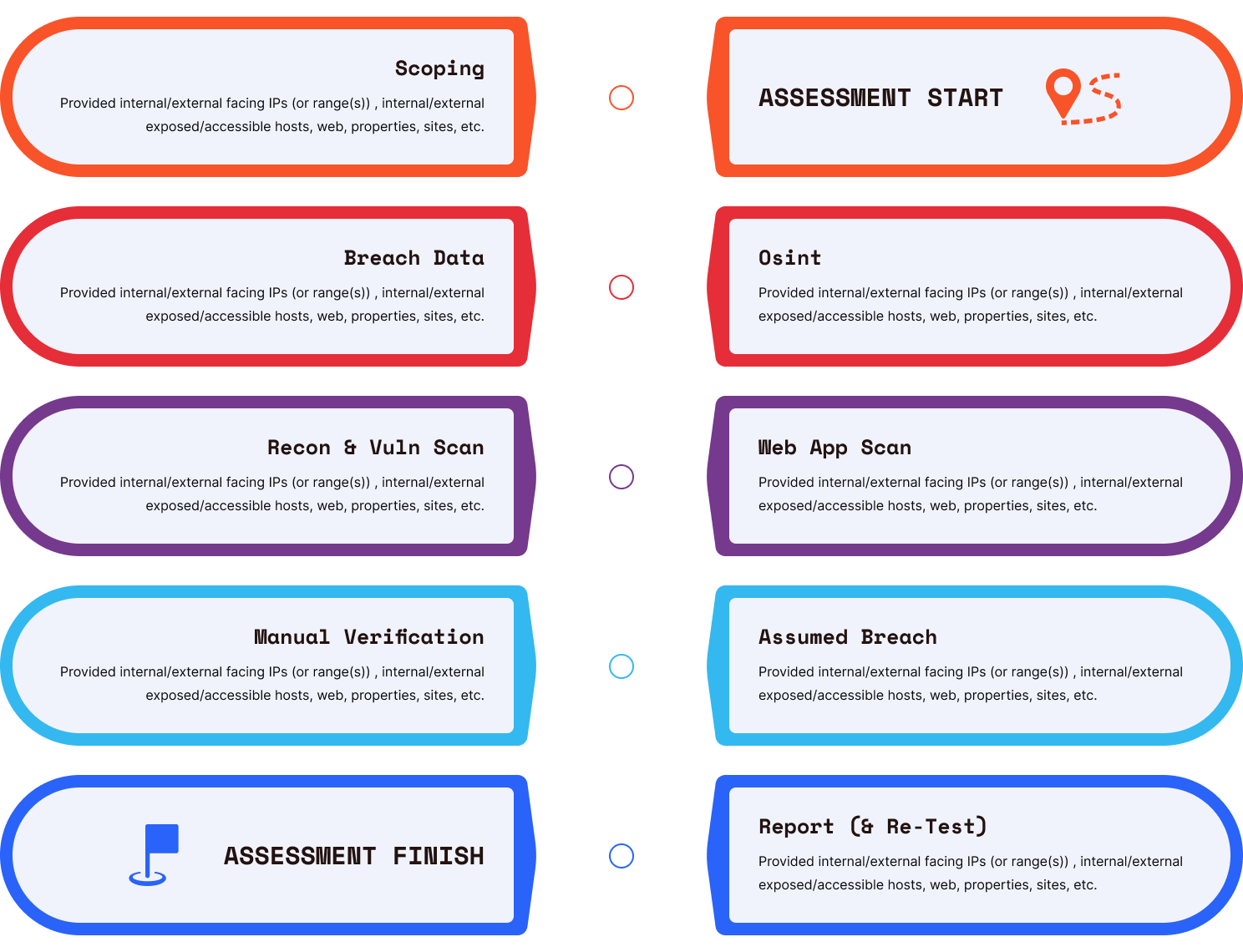
Our penetration testing process follows a structured, manual-first methodology designed to identify real, exploitable vulnerabilities across web applications and APIs.
We begin with scoping and reconnaissance to understand your application architecture, exposed endpoints, and attack surface. This includes identifying APIs, authentication flows, user roles, and critical business logic.
Next, we perform in-depth manual testing of authentication mechanisms, access controls, session management, and application logic — focusing on vulnerabilities such as IDOR (Broken Access Control), privilege escalation, insecure workflows, and data exposure.
We then validate findings through manual verification and real-world exploitation scenarios to confirm impact and eliminate false positives. Finally, we provide a detailed security report with clear reproduction steps, business impact, and developer-focused remediation guidance — followed by re-testing to ensure vulnerabilities are properly resolved.


“Web Application Penetration Testing Services for Modern SaaS Applications”
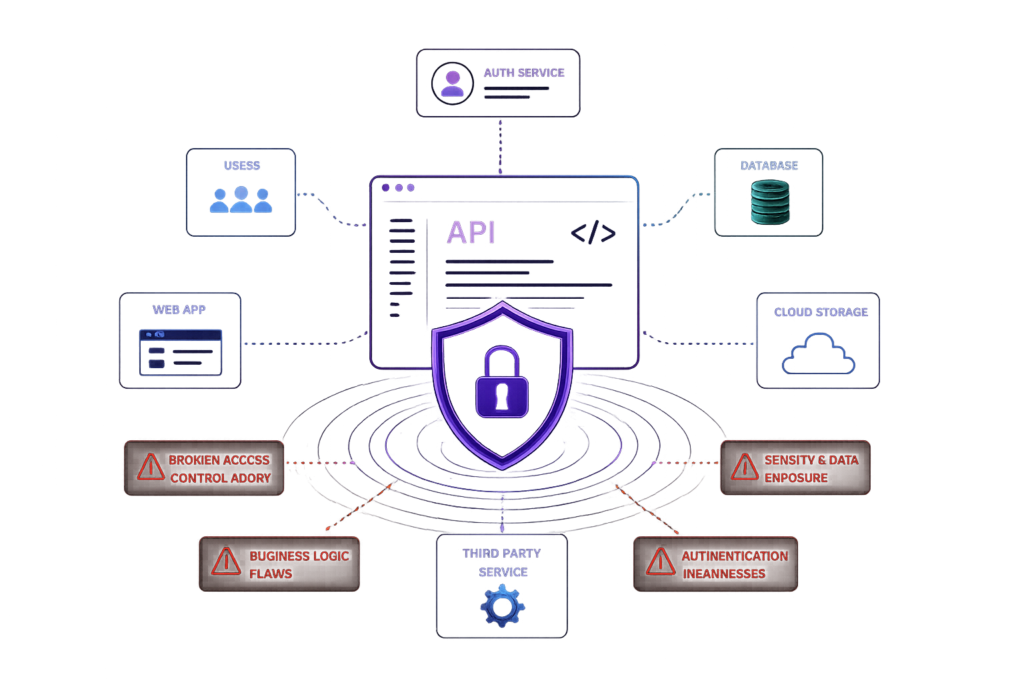
Modern SaaS applications rely heavily on APIs, authentication systems, and complex user workflows creating a large attack surface that traditional security testing often fails to fully cover. Our web application penetration testing services are designed to identify real, exploitable vulnerabilities across modern applications, including web platforms, APIs, and integrated systems.
We test for critical security issues such as broken access control (IDOR/BOLA), authentication and session management flaws, insecure business logic, and sensitive data exposure — the same vulnerabilities attackers actively exploit in real-world scenarios. Unlike automated scanning tools, our penetration testing services focus on manual, in-depth testing of application behavior — helping uncover hidden risks, chained vulnerabilities, and multi-step attack paths that are often missed.
Whether you are building a SaaS platform, scaling an API-driven application, or preparing for a security audit, our testing approach is designed to help you identify real risks, reduce attack surface, and strengthen your overall security posture.

We identify real vulnerabilities in REST and GraphQL APIs that attackers actively exploit — including broken object level authorization (BOLA/IDOR), insecure endpoints, authentication flaws, and sensitive data exposure.
Our API security testing focuses on how APIs behave in real-world attack scenarios, not just how they are designed. We test authorization logic, token handling, rate limits, and business workflows to uncover vulnerabilities that can lead to unauthorized access, data leaks, and account compromise.
We simulate real abuse cases — helping your team understand how attackers interact with your API and where critical security gaps exist.
Common impact: Unauthorized data access, account takeover, API abuse, sensitive data exposure
We identify critical authentication and access control vulnerabilities that attackers use to gain unauthorized access — including broken object level authorization (IDOR/BOLA), privilege escalation, session weaknesses, and insecure authentication flows.
Our testing focuses on real-world exploit scenarios, not theoretical issues. We analyze how users interact with your application across different roles, endpoints, and workflows to uncover authorization bypasses and logic flaws that automated tools often miss.
We test session handling, token security, multi-step workflows, and edge-case behaviors to identify vulnerabilities that can lead to account takeover, unauthorized data access, and privilege escalation.
Common impact: Account takeover, unauthorized access, privilege escalation, data leakage
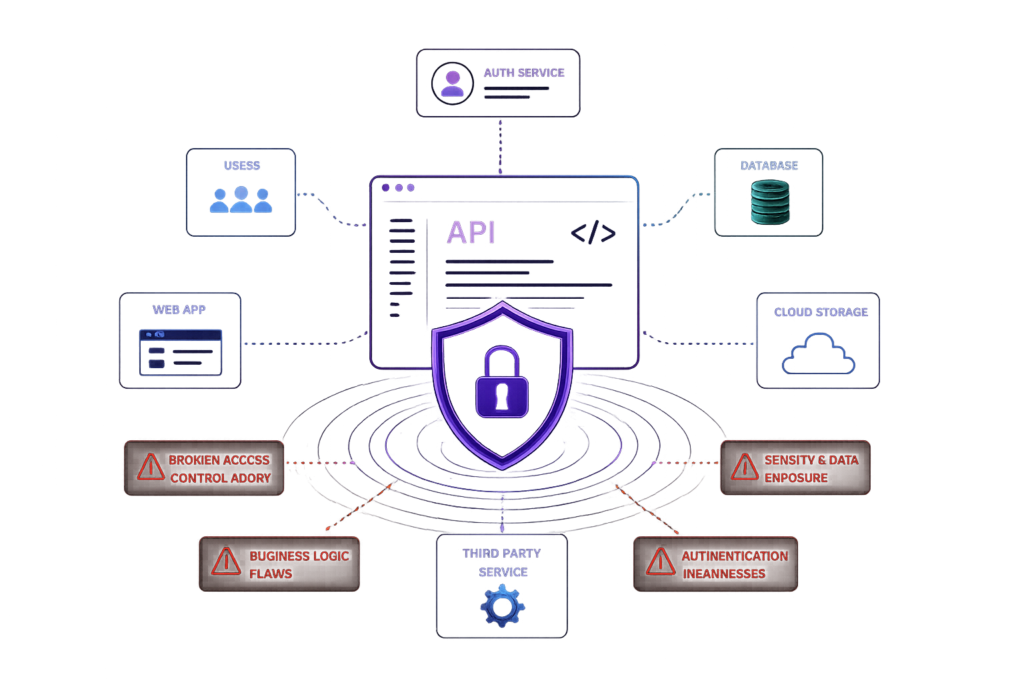
We identify business logic vulnerabilities that allow attackers to abuse application workflows — even when authentication and access controls appear secure.
These issues occur when applications trust user behavior without properly validating how features should be used. We test real user flows such as payments, account actions, onboarding processes, and multi-step operations to uncover logic flaws that can be exploited.
Our approach focuses on how attackers manipulate workflows — including bypassing restrictions, abusing pricing logic, chaining actions, and exploiting edge cases that automated tools cannot detect.
We simulate real-world abuse scenarios to uncover vulnerabilities that can lead to financial loss, unauthorized actions, and platform abuse.
Common impact: Payment bypass, unauthorized actions, abuse of features, financial loss
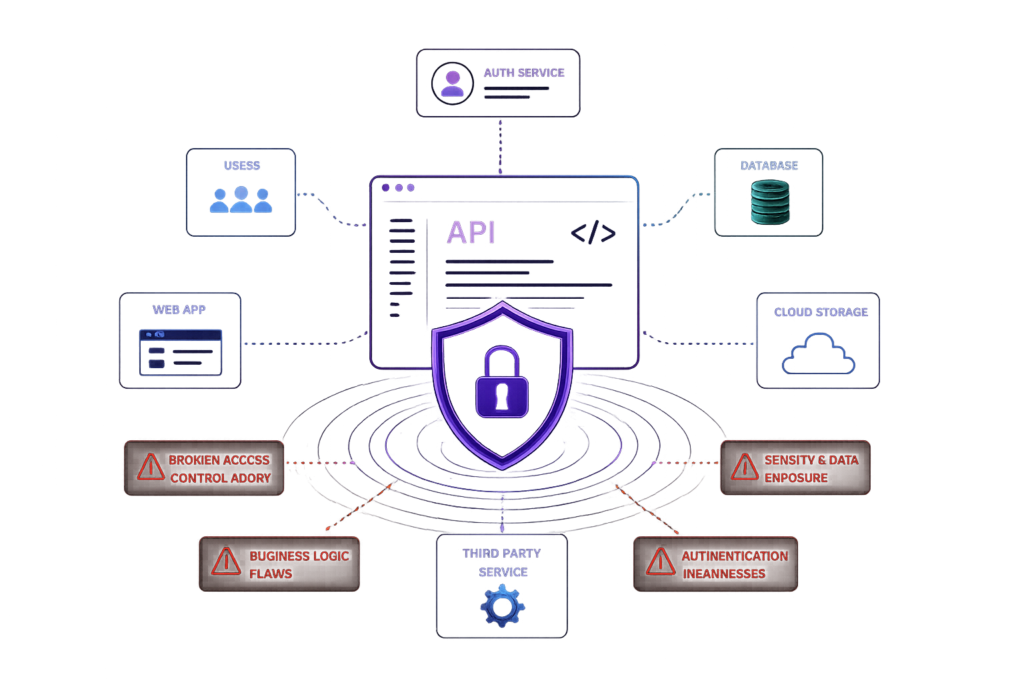
We identify sensitive data exposure and security misconfigurations that can leak critical information or weaken your application’s security posture.
This includes testing for improperly exposed APIs, misconfigured cloud storage, insecure headers, verbose error messages, and unintended data leaks across endpoints and responses.
Our approach focuses on real-world impact — analyzing how attackers can extract sensitive data such as user information, tokens, internal system details, or configuration secrets.
We also assess security misconfigurations across environments, ensuring that access controls, permissions, and system settings are properly enforced and not exposing unnecessary attack surface.
Common impact: Sensitive data leakage, token exposure, internal system disclosure, unauthorized access
Human-focused attack simulations to test real-world security awareness.
We go beyond standard penetration testing by simulating advanced attack scenarios against your application.
This includes chaining vulnerabilities, abusing business logic, and replicating real attacker behavior to uncover risks that automated tools and traditional testing often miss.
Our approach focuses on how vulnerabilities are actually exploited in the wild — not just identifying isolated issues.
We simulate real-world attacks against your web application, APIs, and authentication systems to identify exploitable vulnerabilities.
This includes testing for:
Unlike automated scanners, our testing focuses on how attackers actually exploit these weaknesses.
Vulnerability scanning uses automated tools to detect known issues.
Penetration testing goes deeper — manually testing application logic, user flows, and access controls to uncover real, exploitable vulnerabilities.
This is where issues like IDOR, privilege escalation, and multi-step attack chains are typically found.
Yes. Our penetration testing is focused on modern SaaS platforms and API-driven applications.
We specifically test:
Yes. One of our core focuses is identifying vulnerabilities that lead to account takeover.
This includes:
We test real attack paths — not just isolated issues.
Typical timelines depend on scope, but most web application penetration tests take:
We prioritize depth over superficial coverage.
You receive a clear, developer-focused report that includes:
No noise. No automated scan dumps.
Our penetration testing services are focused on uncovering real security risks — not generating generic reports. We identify exploitable vulnerabilities such as IDOR, authentication flaws, and business logic issues that lead to account takeover, data exposure, and real incidents. No noise. No automated scan reports. Just actionable findings your team can fix quickly. Request a Web Application Penetration Test and understand what attackers would actually find.
You’re not just getting a report — you’re getting real attack insights.